













We have more on cameras that we just haven’t shared as yet. But we will in due time. Why? Because there are improvements all the time and also creativity with innovation.















We have more on cameras that we just haven’t shared as yet. But we will in due time. Why? Because there are improvements all the time and also creativity with innovation.
Beyond the traditional to modernized forms of cameras for image capturing for leisure, events and professional use in compact all the way to DSLR.
With the improvements in technology providing better resolution (Measured in Pixels now in the megapixel), better lenses, miniaturization (giving smaller foot print), better sensors (Low light, low lux sometimes even refered to as starlight sensors), better storage mediums, accessories and much more. Shows are being made using these cameras in tandem with better software tools for maximising the benefits of what was captured for all forms of image capturing be they stills, moving motion or all the in between and over image forms.
To the dismay of the hardcore professionals, the term could be applied to almost everyone and the ability could be secured just as easily for the needs of most. Its till the deeper studied skills are required, then can the professionals be separated from the ones whom just had good tools.
But to the delight of the overall users these new miniature cameras can be used in still and moving conditions. All that is necessary is to look for the right size and price. Then add on accessories such as brackets, lights, harnesses and much more. A more prominent reference to them are action cameras or body cameras.
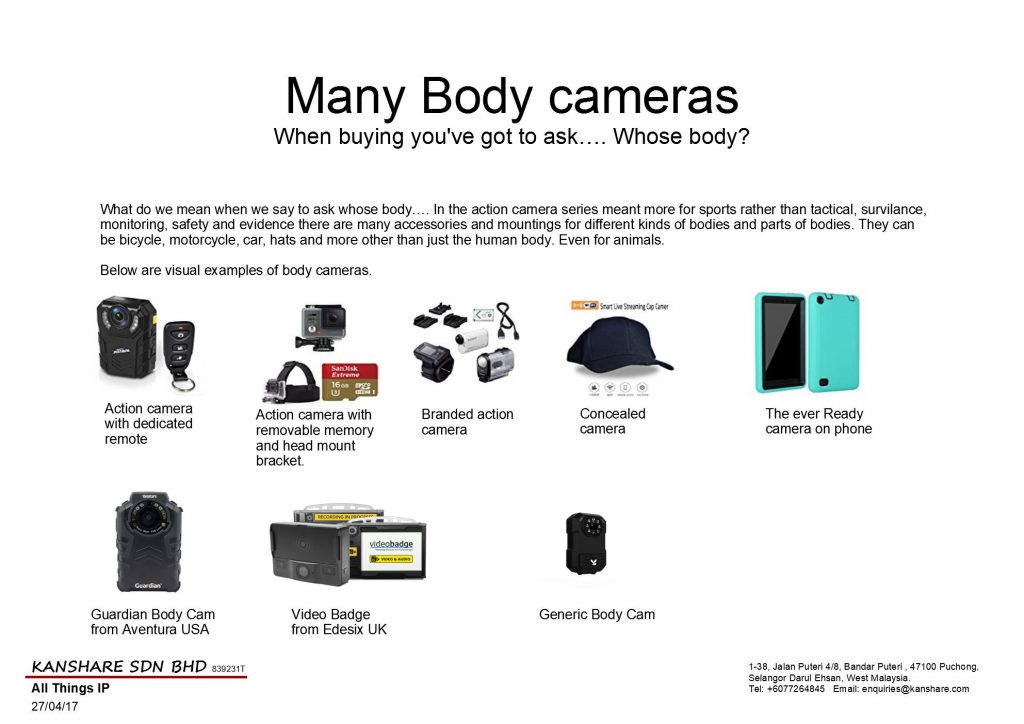
The above are some samples of these miniature mobile cameras.
Note beyond the standard measures as described earlier. Some of the more discerning features are if they are stand alone devices that you need to remove the images with a cable or they have removable memory cards.
Or that they have network features. That is that it can connect via bluetooth, IR, RF, Wifi or mobile telephony network (GPRS, 3G, 4G, LTE etc) directly.
Controls on board, supplemented with software controls via pc, remotes (Wearable options), Local app on Smart device (smart phone/tablet) direct to device, App on smart device via the internet or any other remote access network support.
But even these remote accessible cameras have controllers that do control or remote access by singular device. Multiple device view and controls are normally features available in higher end models and purpose, The most widely used application is body cameras for security and safety application. Much like cctv that is mobile.
The industries that are starting to consider using it or have started deploying are generally security (Both public and private). However its application is much wider.
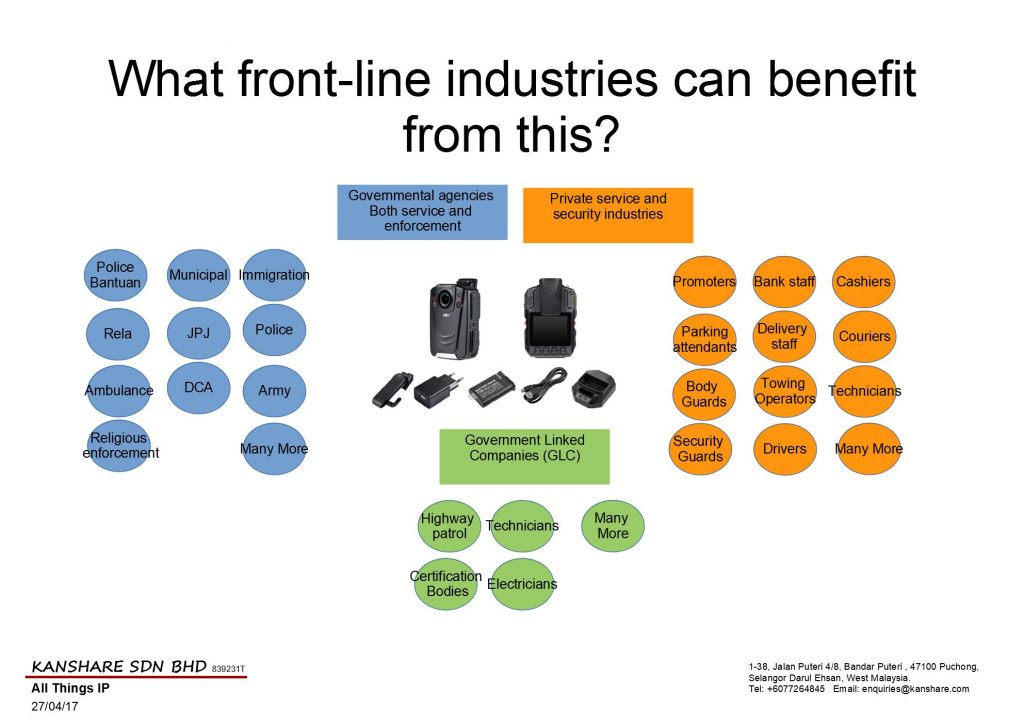
Note some of the applicable organisations are refered to in some cases by industry, skill area and even specific departmental organisations mostly relevant in Malaysia. But in other countries these agencies could exist if not the role within other agencies but named differently. The important thing is to note that in this day and age protection and proof is becoming increasingly more important. More and more demands are arising from very unique stake holders.
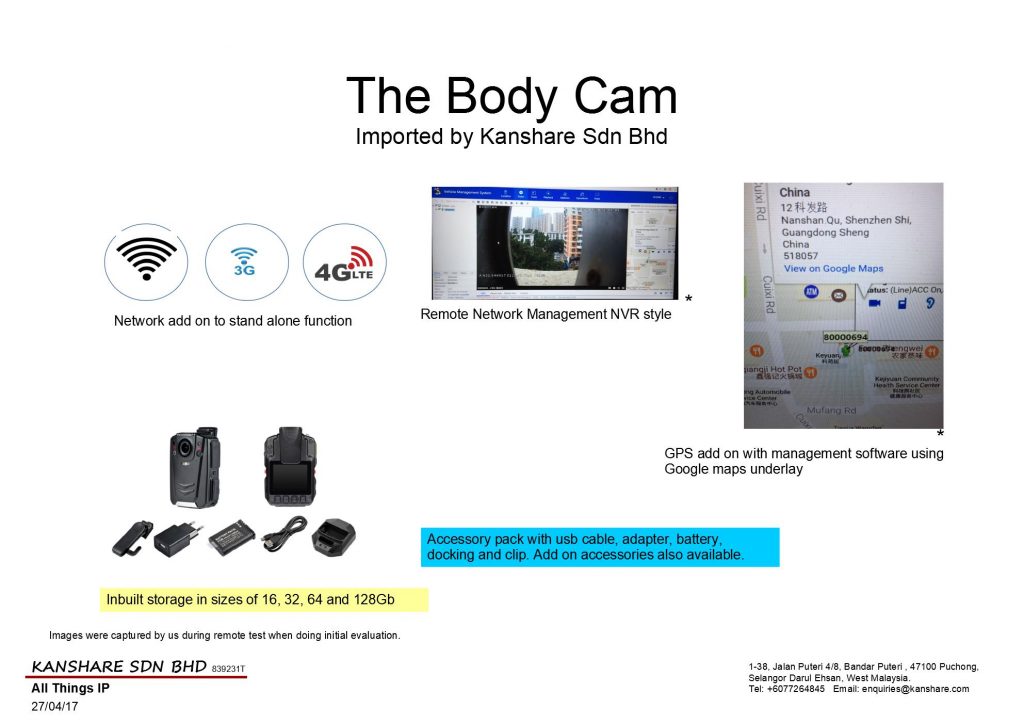
Kanshare Sdn Bhd has done extensive research through our normal stages in our evaluation process before taking on products and product categories before suggesting or recommending their usage. The above is a body camera that can function in stand alone non networked mode all the way to the latest IP network connectivity and communication.
Below are some of the applications in just one industry area. Security.
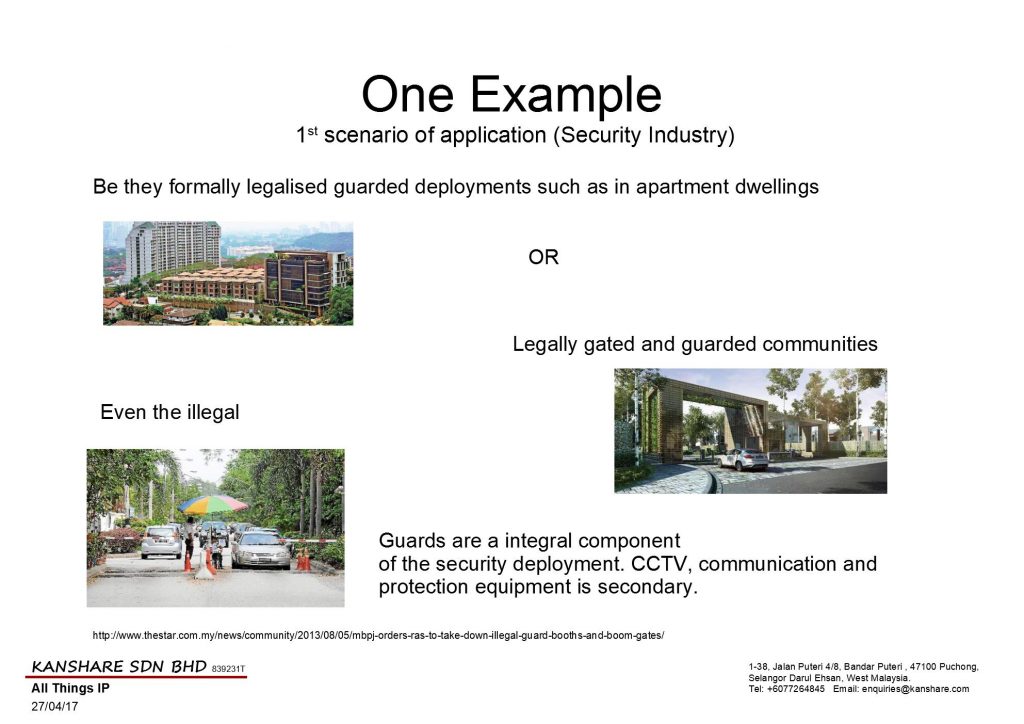
In tjhe examples above this solution can be applied or deployed in tandem with the static cameras and have the benefits of recording all the footage centrally for viewing or tracing purposes and more.
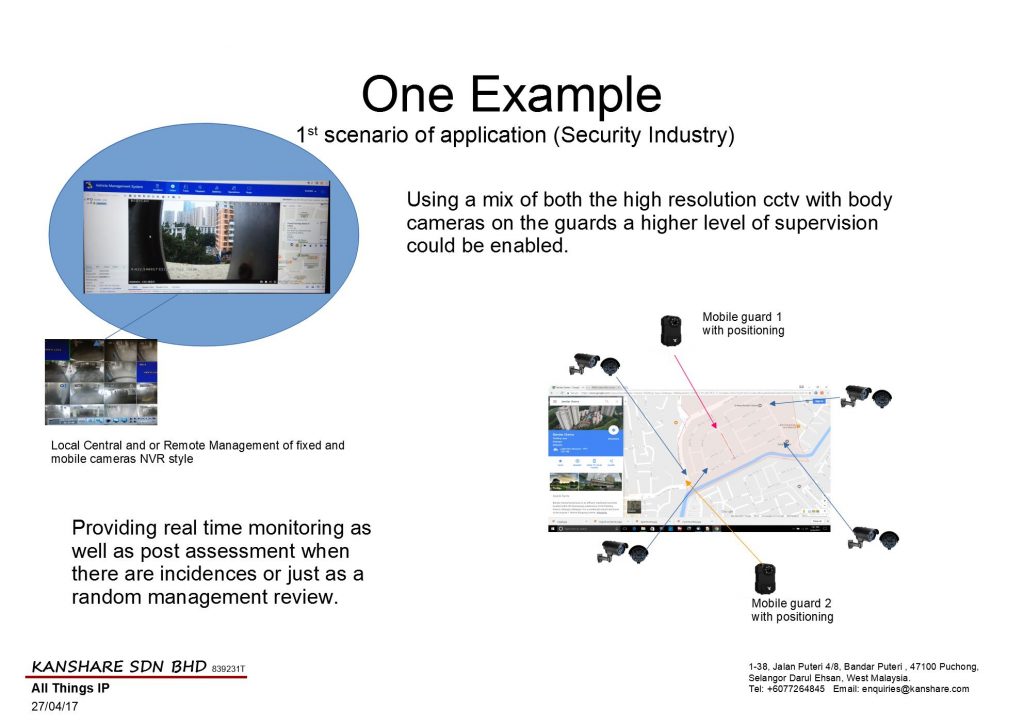
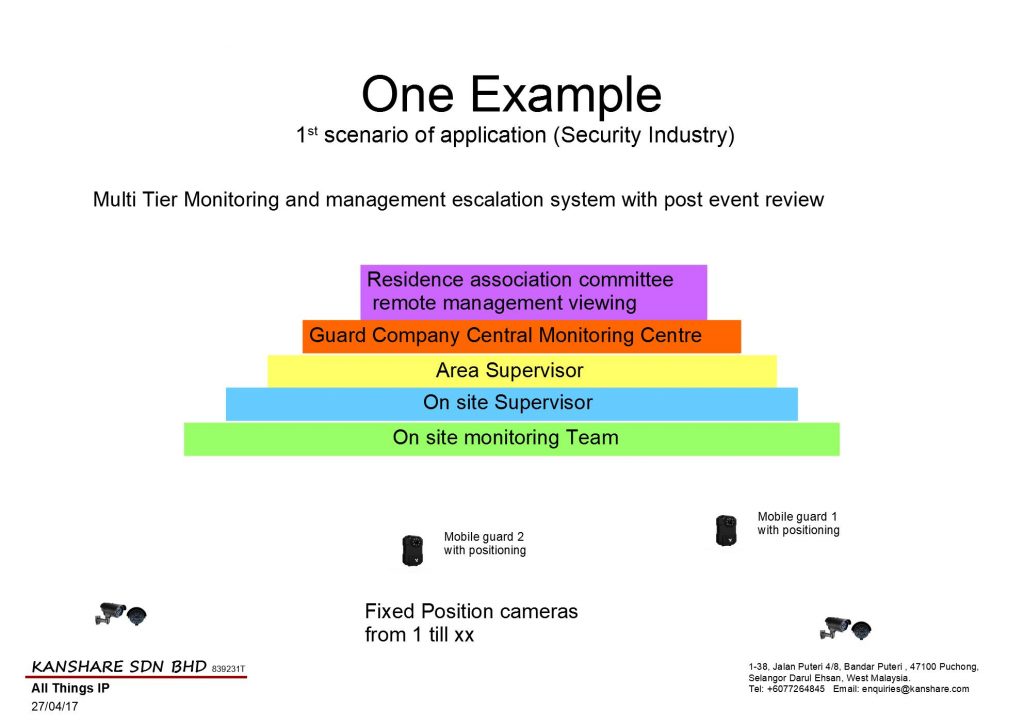
This example usage can also provide multi tier control and observation for action. Below are some stake holders that could be addressed with different levels of access and capabilities according to relevant need.
With that deployment some issues can be addressed over and beyond the written reports based on statements of visual observations of a singular person or group of persons that cannot be produced for review beyond that reported information.
One interesting observation when choosing a product is that though many have network access and control, storage (either removable or onboard or both). Control software and GPS.
The more advance versions can do multi control and provide ability to generate reports. The better it is the process is a matter of choosing whats appropriate for you with out setup requirements. (choice of relevant information is a check on or off method). When setup is required it is flexible enough to do drag and drop selection to create your report requirement. Preferable picked once, saved and repeat with a click of a button. The least user friendly versions require that you actually code even for the simplest presentation of information captured or stored.
The better advanced body cameras are now becoming a replacement to the standard walkie talkie to provide an upgrade in communications with whats becoming a standard offering of PTT (Push To Talk) functions much like a walkie talkie. But what makes it better is the ability to differentiate the user by actual id beyond the traditional call signs. With the use of unique user logins, password protected upwards to rfid and biometric ids. Supported by deep ai functions such as voice recognition and matching back ends this provides much better accountability of usage and access and time stamping.
The GPS Support now comes beyond just standard GPS or A-GPS, but also the russian version Glonass and the Chinese Beidou variations for cross comparison accuracy and fail over protection.
Man down function is another great function these body cameras have which generally uses a combination of the gyro function in the device, motion on a physical basis but also on image and audio surrounding the device to provide user protection in event of illness, accidents or even attack.
With two and multi camera, PTZ head cameras, smart support detection (for non moving objects such as in conditions for bomb protection, object count in asset and inventory count, path mapping (visual path or multi camera spotting path tracking), entry and exit tracking, facial recognition and much more.
The future in this segment of camera usage is very promising and exciting.
We are all familiar with the normal standard walkie talkie that we see guards, stores, restaurant, police and many other agencies or groups using.
What we may not be familiar is that they are mostly controlled items as their primary build and use was for enforcement. Their larger and longer range cousins were for military and defense usage.
Now the traditional walkie talkies go over the air either in analog or digital forms. There are some variations such as over the satellite.
Over the last few years with the increased usage of internet and the conversion to wider spread of internet usage with its terminals. Walkie Talkie functions have also had a migration across with many methods. The most widely spread version is on the IMS platform. Specifically the PUSH To Talk system. In some sense it is like a digital intercom except it can go one to one and one to many.
The presence of this function is in many Chat applications and other dedicated built applications. The hard ware need not be specialised. But there are specialised hardware available for those whom prefer specialised hardware.
The for public use especially the licence not required category normally has a small throw of below 5km. Further than that a licence is required per device and only trained users with licences to use can own and use the units. Other person allowed to use would normally be enforcement personnel.
So with the short range limit or licenced required for device and operator higher range variants, what you may end up with would be clusters of connected persons then needing to swap to a mobile phone or land line for longer distance communication.
PTT in its bearest state just needs data networks based on IP (Internet Protocol). So it can be hosted on wifi, mobile internet and data over satellite.
PTT could be in one group or a one to one communication of known users.
The friendly part of PTT even if you are in one site. You could also create purpose/role/responsibility or other reasons for grouping. Even within one site. And a single user can belong to many groups.
With above configuration of usage. You can also extend the usage to multi sites. Same features. But as different groups. And number of users could belong to groups from other sites too.
Now the traditional sets would have cost a huge amount of money. As such to switch over can be a barrier. Also having too many different technologies that dont talk to each other could put off any sane user.
However there are solutions to integrate the old with the new. As in the case with either embedded gateways within the device or separate gateways per site.
With this you would retain the ability to use the old sets using unverified call signs and unverified locations. With the current by user login, password, gps position with visual verification by video and still image new technology PTT (internet walkie talkie).
The best part is that the technologies can mix and the features can be extended within the environment even down to putting digital fences using GPS and other positioning tools. Hence creating what is called a geo fence. This can be used in a positive manner of providing notification to the user that he is partroling further than his agreed area. And for the central monitor that the user has exceeded his area of partrol which could mean something that is bad has happened. And with the right device have even control to remote enable camera, communication and more for verification that the user is fine.
For KANSHARE SDN BHD. We have a new principal and partner that provides us ruggedised versions of this solution in a smart phone walkie talkie format and also other providers whom provide it within a body camera format.
Types of users and industries
Interested in the solution?
email us at enquiries@kanshare.com
Introduction
The risks of valuables transportation services (cash, jewelry, intellectual valuables etc) along with valuable replenishment services (ATM cash replenishment and retrieval) to name a few are high as are the cost for the services.
Specifically Cash In Transit (CIT) or the service activity of transporting money for legal entities is a large business due to the level of risk. This normally requires many factors to reduce those risks. But with cost as a consideration viability normally could reduce the measures that are taken. Thereby directly increasing the risk.
The task normally consist of the pick up activity (This is where verification actvities and accountabilty take over activities are carried out.), the actually transportation activity (This would be remaining vigilant, Protecting, driving and avoidance) and finally at the destination is the Handover activity (where verification again take place, accounting and transfer of responsibility)
In Malaysia additional activities that are also outsource to guard companies the actually loading of money into ATMs. Hence even more risks are exposed.
Risks
Some of the risks that arise are : –
Any activity dealing with cash or valuables and not handled by the owner themselves bring about the following: –
Addressing the Risks
Even though the activity may bring risk the rewards can also be fulfilling for the right people. To ensure the risk is worthwhile and to reduce them some measures must be taken. The following are the ones taken today:-
Raising the Bar
In addressing the act of raising the bar beyond the cost of vehicle, fuel and man hour rate, There is more to be provided with justifiable cost increase but higher benefits in terms of security and possible reductions on other protection received as rewards in reduced insurance premiums and more for the companies involved.
Tool, Tracking and Reporting (TTR)
Though there were 4 other items of main issues and measures needed to be addressed , we will only deal with the fifth one which is Tools, Tracking and Reporting. Though it is not said that there is none today (And there cannot be no measures in place), the measures used could be updated and upgraded to increase transparency, insert digital tracks with alarms when conditions not met and reporting of the overall activity (in action and when action completed).
The three main components to be enhanced is the vehicle traceability, the cargo with path validation and personnel support. This by tagging with real time tracking visually, audio and GPS positions. of all components involved in the service/activity.
With all those components in place the hidden or unknown better yet described limited information for verification previously available possible due to technology. The increase of it in tandem with the tried and proven processes, illuminated by the current availability to provide real time viewing with evidence (real time and post time) of the service being carried out.
But not withholding the best improvement yet, the ability to provide remote support when the risky events occur. Such as calling in relevant personnel and parties when robberies or interception of the valuables occur.
This in itself will increase the risk factor to the criminals and increase the safety factor to all provider personnel and customer valuables.
But though it may improve capabilities. It does not eliminate the original risks at all.
What to know more about the solution or have a quotation for implementation? Email us at enquiries@kanshare.com
Note the products and solutions displayed are provided by manufacturers and distributors as products for our reselling and deployment in solutions designed in part or integrated as a whole from one or many ideas.
The brands or indicators/inference of a particular brand does not mean that the solution or component for that part of the solution can only be delivered by that brand or inferred brand.
Cost, preference and other factors may drive variation to the frame of ideas elaborated above.
CCTV systems have increased in the features that provide for specific functions. They range from low light (IR or sensitive CCD/CMOS sensor), facial recognition, stock count keeping automatically updating the stock levels, to motion detection and many more features.
Today the latest entrant to those features is temperature and humidity monitoring. This is especially useful for environments that require the ability to capture and monitor these changes. Industries that can make good use are from farming to monitoring environmental changes to sensitive products such as wineries, rooftops, computer rooms, telecommunication centres, utility centres and more.
More coming soon on this topic.
Latest update contained in this link
This is a follow on from our previous article CCTV Basics http://kanshare.com/Solutions/cctv-basics-ip-cctv/
Today is about power and video. First is power. Everything needs power.
The most basic CCTV setup is the distributed power setup. This is easier as you grab power from the nearest socket or extend from the nearest power socket or lighting point.
The next format is the centralised power supply system. This requires wiring from camera all the way back to the central power supply. Generally you drag one cable for one camera. There are occasions some may split the power to cameras along the way. But this method is the surest way to having problems in the long run. In terms of trouble shooting and also the more technical which is power drop.
Below are the types of cables that can be used for a power solution for CCTVs. But they all have their particular use, methods of use and characteristics. A little more descriptions as enclosed in the slide.
Now as power has been provided separately. The choice of video transmission is equally varied. And basics limit the options to the relevant technology. But in over the years innovative solutions such as transmitters receivers, converters and baluns have allowed cross transmission of video on different cable and wireless solutions.
Even further creative uses of older technologies have even provided the single wire solution for both Power and Signal. And they totally differe from the analog twin signal and power cable.
These technologies actually transmit the both the power and signal over the very same cables.
POE. Power Over Ethernet uses the friendly computer cable to make connection between the recorder/viewing station. As the name says there is power and signal transmitted over the ethernet cable with RJ45 connectors.
PLC Power Line Communication or sometimes known as the HomePlug. Transmit both the video and power over the normal house power line. Very stable. Hardly any wiring required in addition to whats there.
POC/EOC Power Over Coaxial and Ethernet Over Coaxial. Now the former is relatively new as traditionally you did not send power over any coaxial cables. Reasons very obvious which you can read up more on the purpose of cables and their types. (You could wiki it and more. Maybe we will do a little write up in the future.) The later Ethernet Over Coaxial is relatively old as it is similar to the token ring network with the exception of the speed and the finickiness of token ring which required very strict cable types, lengths and terminators on each end.
We have written a little bit about this in brief for our customers. But soon there will be some publishing on this here too. Look out for it.
All in all to sum up, the security market today is beyond national deployment in the more staid governmental policing and army. Nor is it the sole commercial controlled security services industry which requires trained personnel (which it used to have and abundance of source in the past. Today they require huge investments into training which is sometimes daunting).
You now have an array of solutions to put part of the monitoring of your security in your hands. And to support the organised bodies to enhance their reach to keep everyone safe.
Got a query or need? Email us at enquiries@kanshare.com.